How to use Security Center to make your WHM server as secure as possible
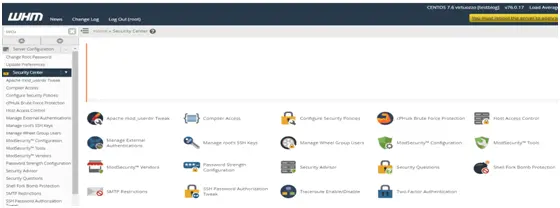
WHM’s ‘Security Center’ provides you with a number of tools to prevent your server’s security from being compromised as well as some ways to combat any malicious person that causes you problems.
To begin, Scroll down slightly to the ‘Security’ Category of the menu. Click ‘Security Center’.
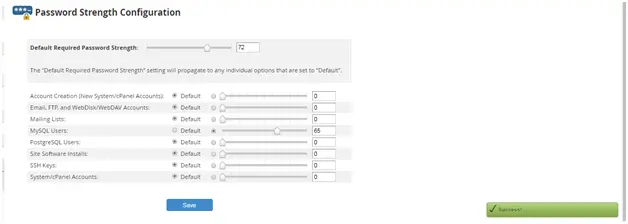
The first page in the ‘Security Center’ allows you to change the minimum required password strength for each area of cPanel and WHM that accepts a Password. Let’s take a look. By default WHM and cPanel do not enforce minimum password strength. Enabling this can help prevent users from setting easy to guess passwords depending on the settings you specify.
Click the checkmark hereto enable this feature: Default Required password strength.
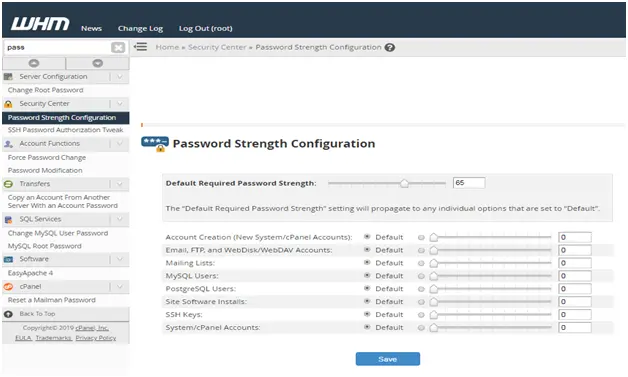
Now drag the slider over to the desired setting or type a number at right.
While it’s true that putting the settings at full strength can cause frustration for your account owners. The key here is to balance security with sensibility.
The default settings are applied globally to all the password types listed below. You can consider each one on a case by case basis if you want.
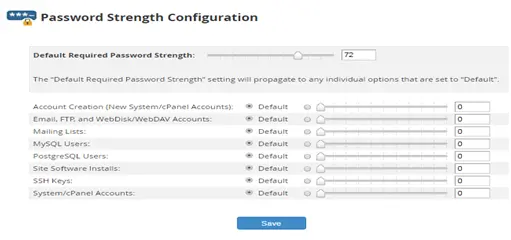
Scroll down.
The majority of your clients are going to store their MySQL passwords in configuration files and not use them frequently we will customize the settings for that type of password.
Click the checkmark to stop it from entering a default value: Required Password Strength for MySQL Users
Then choose a new minimum strength. Several other passwords here should probably be stronger than average but we will leave that up to you.
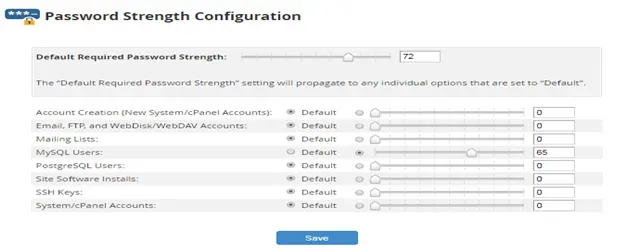
When you are done, scroll down. Click Save.
Return to the security center.
Another important security feature of WHM is ‘CPHulk Brute Force Protection’– This feature helps prevent malicious forces from repeated guessing your passwords until successful. Click here: CPHulk Brute Force Protection.
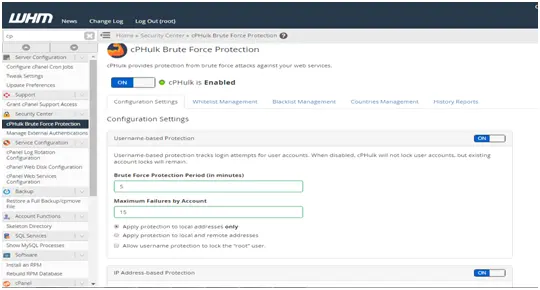
This should have been enabled during initial setup but ours didn’t stay that way for some reason.
Click the ‘enable’ button to fix that. There are a number of settings you can customize for CPHulk, but the defaults should work just fine. Scroll down. The trusted Hosts list page allows you to list hosts and IP addresses that should never trigger the CPHulk protection.
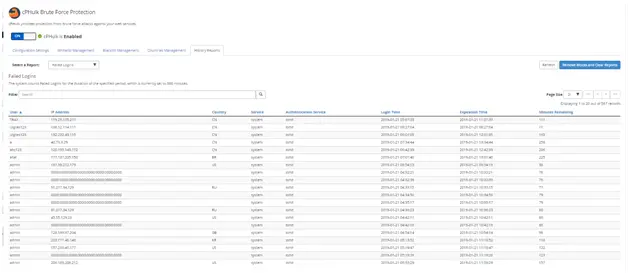
Below you will also find a list of all failed logins..
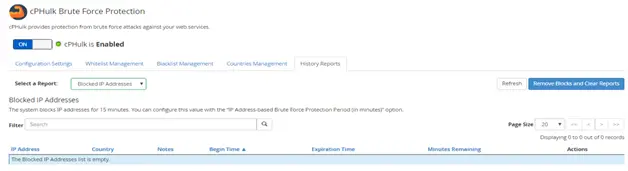
As well as all blocked IP addresses
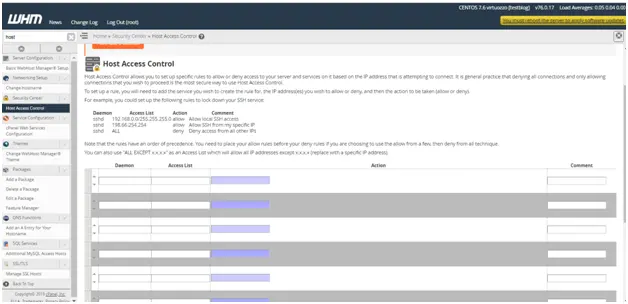
‘Host Access control’ – enables you to allow or deny access to your server or specific services based on the IP address of the incoming request.
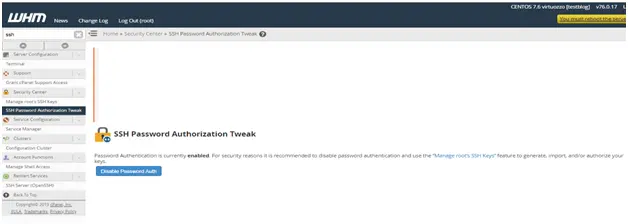
With ‘SSH password Authentication Tweak’ you can strengthen security by disabling password authentication for SSH connections.
‘PHP open_basedir protection’ – should in most cases be turned on.
It will prevent the use of PHP to access files outside of a user’s home directory.
‘The Apache mod_userdir Tweak’- allows you to prevent users from getting around your bandwidth restrictions.
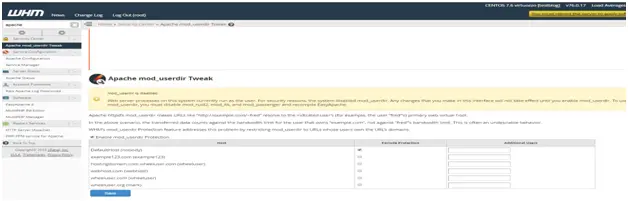
Note that both the PHP and Apache tweak allow you to lift the restrictions for certain users or websites. The compiler for unprivileged users will not need or want access to the compilers so it’s safe to turn this off. You can make exceptions for certain users, if needed.

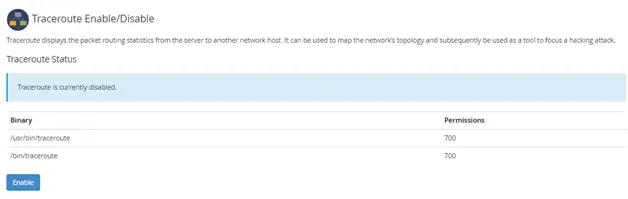
Your system’s ‘Traceroute enable/ disable tool’- can be used by a hacker to gain information. This is disabled for unprivileged users by default and you should have no reason to enable it.
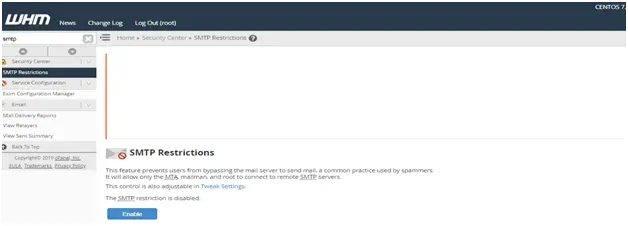
Enabling the ‘SMTP Restrictions’ – will prevent spammers from bypassing your outgoing mail server to send spam.
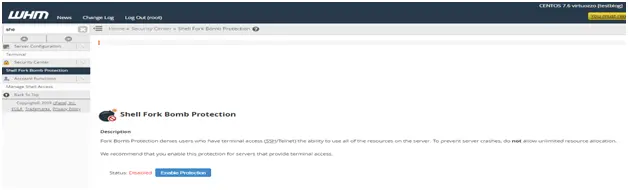
The last item on this page is ‘Shell Fork Bomb Protection’- You should definitely enable this if you intend to give any users shell access with their accounts as it will help prevent them from using up your server’s resources.
You should now have a good idea how to use everything in the security center to make your server as secure as possible.
Visit: Hostdens!

You must log in to post a comment.